new in 2.0: SSLstrip2 for HSTS bypass Image capture with Driftnet TShark for command line .pcap capture …
Continue Reading about mitmAP – Create Fake AP and Sniff Data →
Your treasure of information!

new in 2.0: SSLstrip2 for HSTS bypass Image capture with Driftnet TShark for command line .pcap capture …
Continue Reading about mitmAP – Create Fake AP and Sniff Data →

Rattler helps identify which application DLL’s are vulnerable to DLL preloading attacks. In a nutshell, DLL preloading attacks allow you to trick applications into loading and executing malicious …
mini-tor is a proof-of-concept utility for accessing internet content and hidden service content (.onion) via tor routers. this utility is aiming for as smallest size as possible (currently ~47kb, …
Continue Reading about Microsoft CNG/CryptoAPI Tor Protocol Implementation PoC →

Android Remote Administration Tool AhMyth consists of two parts : Server side : desktop application based on electron framework (control panel) Client side : android application (backdoor) …
Continue Reading about Android Remote Administration Tool: AhMyth →

ACLight is a tool for discovering privileged accounts through advanced ACLs (Access Lists) analysis. It includes the discovery of Shadow Admins in the scanned network. The tool queries the Active …
Continue Reading about Advanced Discovery of Privileged Accounts: ACLight →
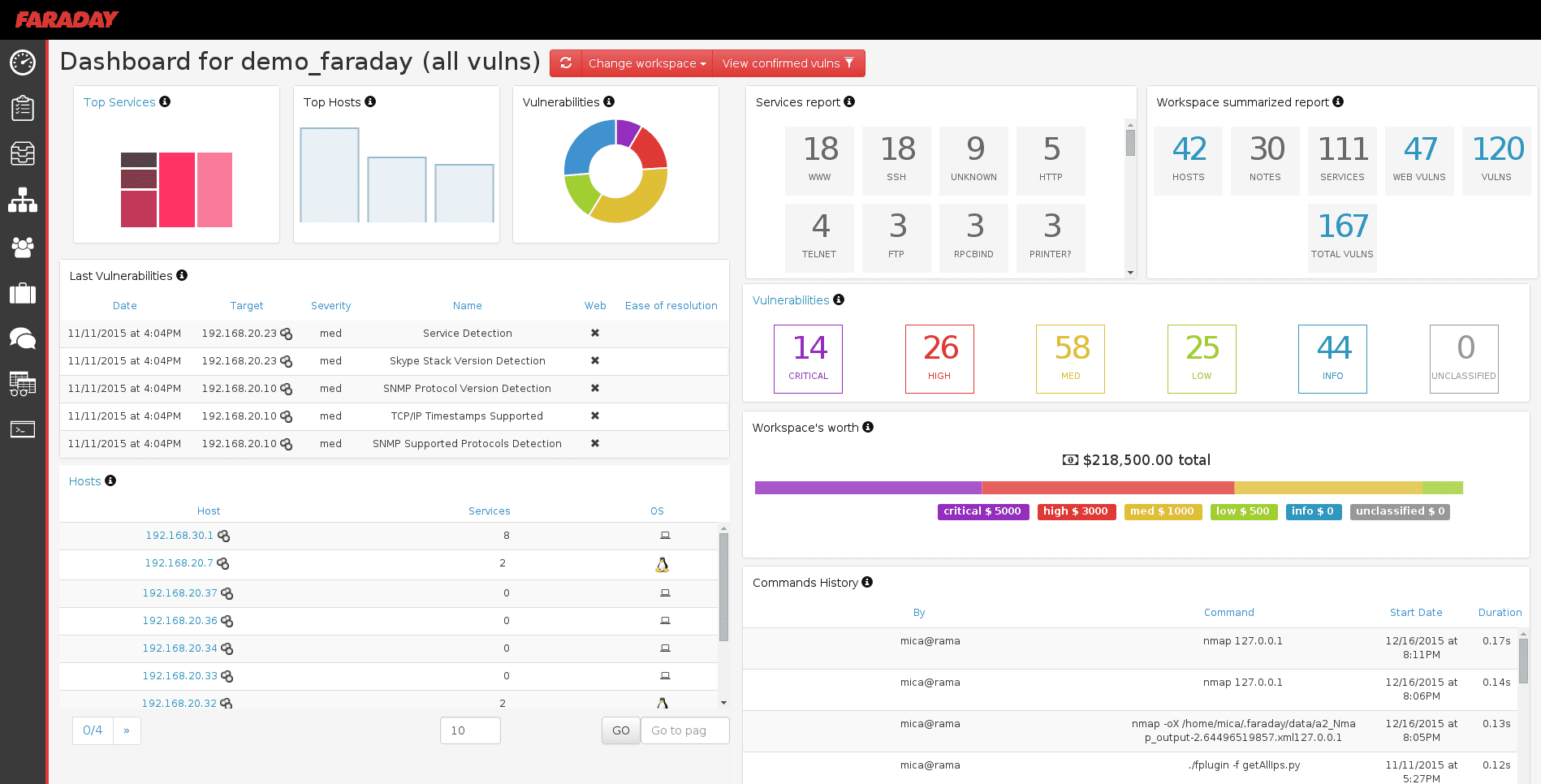
Faraday introduces a new concept – IPE (Integrated Penetration-Test Environment) a multiuser Penetration test IDE. Designed for distribution, indexation and analysis of the data generated during a …
Continue Reading about Faraday v2.6 – Vulnerability Management Platform →