We are going to share with you only the best Chrome extensions used for pen testing. Check all of them below, get informed on what they can do and how can the extensions come in handy, when your pen testing. If you find this “best of” category informative, you surely will love our other Cyber Security guides. Enjoy!
Wappalyzer
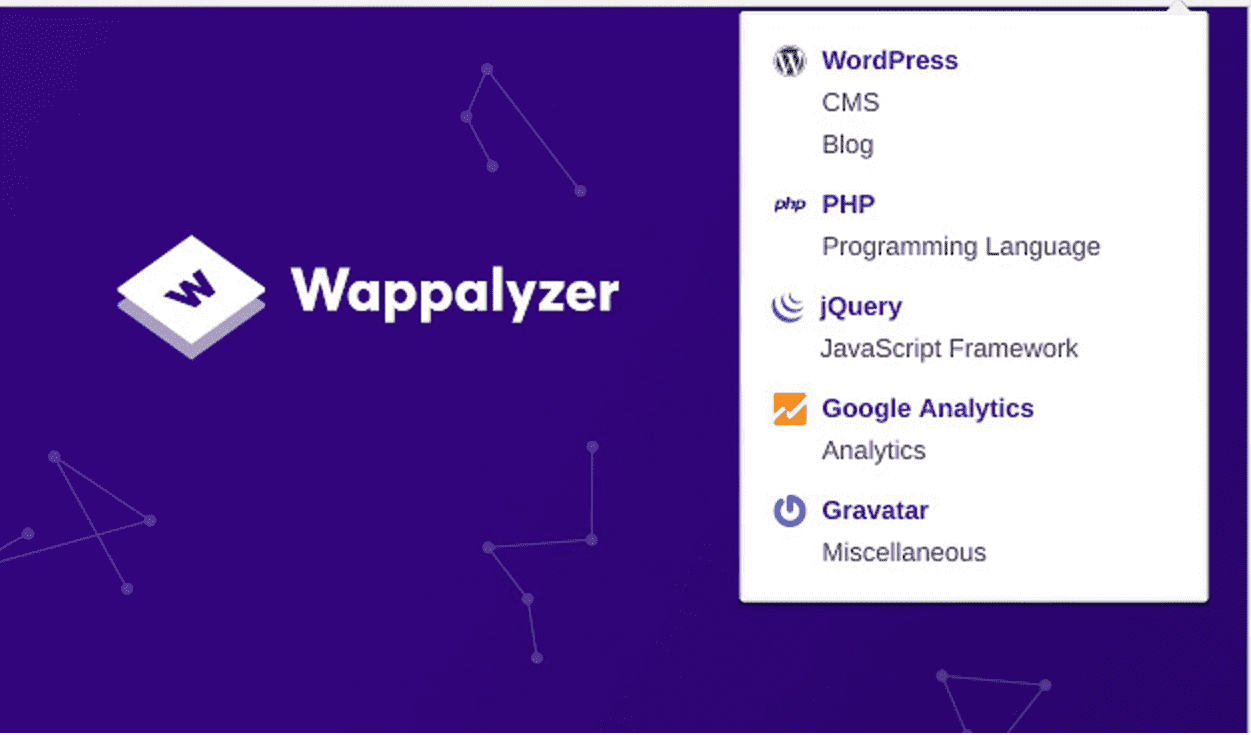
Wappalyzer was created Elbert Alias in 2009 and it is one of the best cross-platform utility which uncovers what kind of technologies a website uses. It can detect e-commerce platforms, server software, content management systems (CMS), web frameworks, analytics tools and much more.
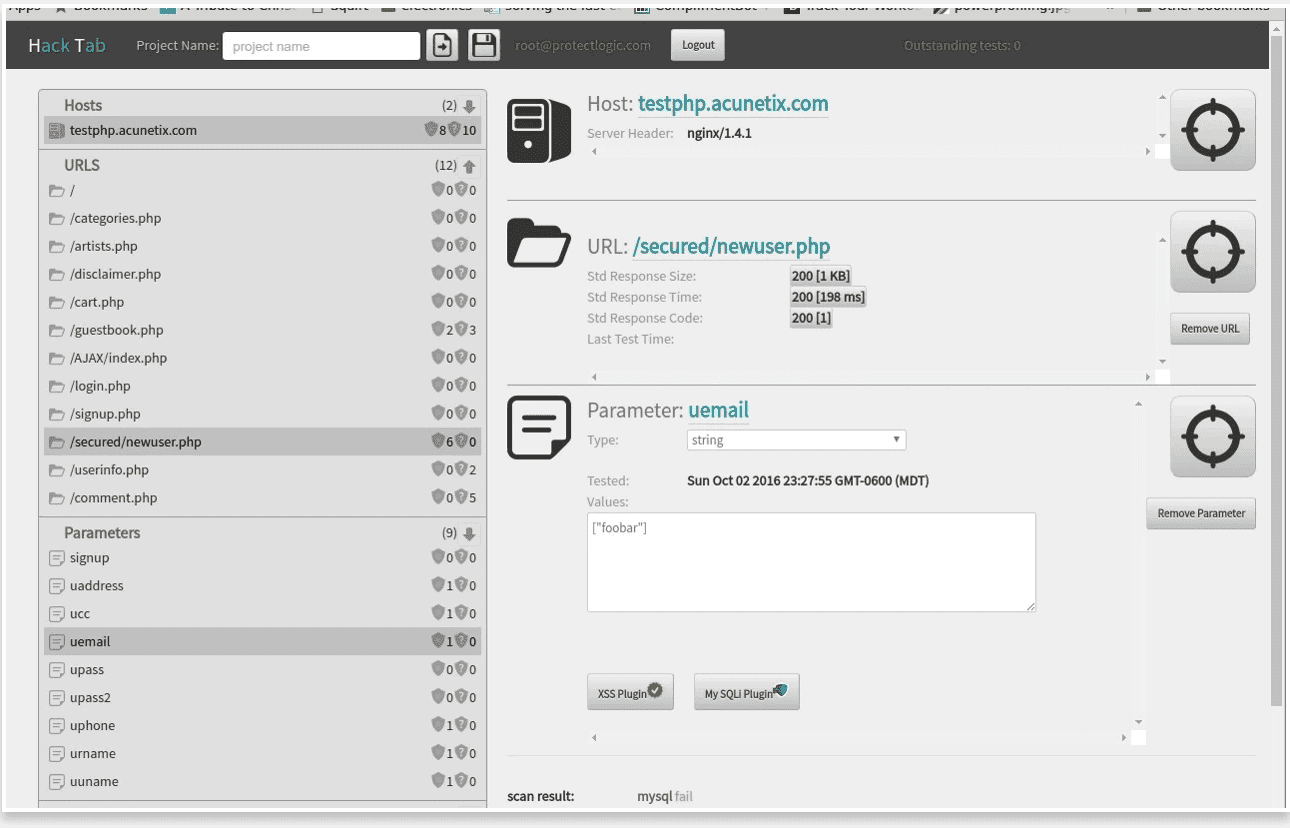
Wappalyzer can detect 1,109 web applications in the following categories:
You can also analyse a website in real-time at their website, if you don’t really want to install the extension.
For more information and link to install it, visit Wappalyzer.com
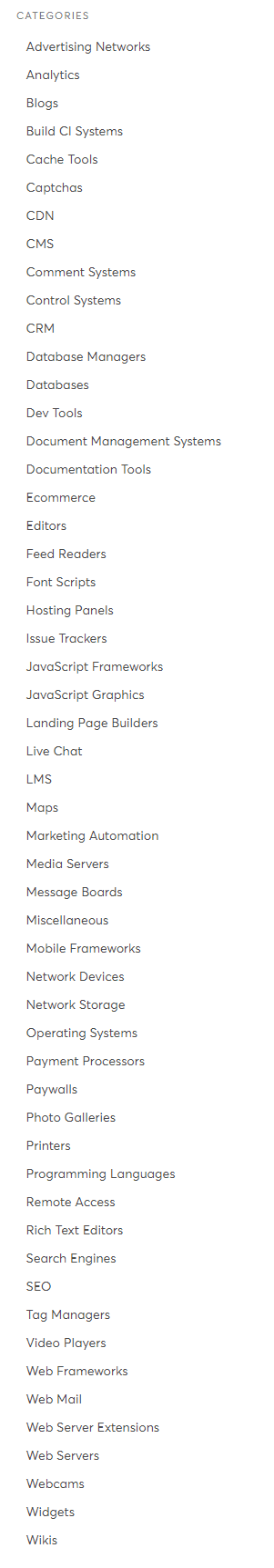
Hookish
“Hooks in to interesting functions and helps reverse the web app faster.”
It’s just like a Swiss Army knife of Advanced Pen Testing of web clients. It hooks into web app’s DOM and it also lets you analyze the web app’s more effectively.
Features:
- Hook multiple DOM sources and sinks
- Unsafe anchor tags (target=_blank)
- Statically analyze any web page for Javascript issues.
- Hook WebSocket responses.
- Hook XHR requests and responses
- Show function call trace.
- Hook XHR responses and correlate with DOM mutations.
You can find the GitHub page here.
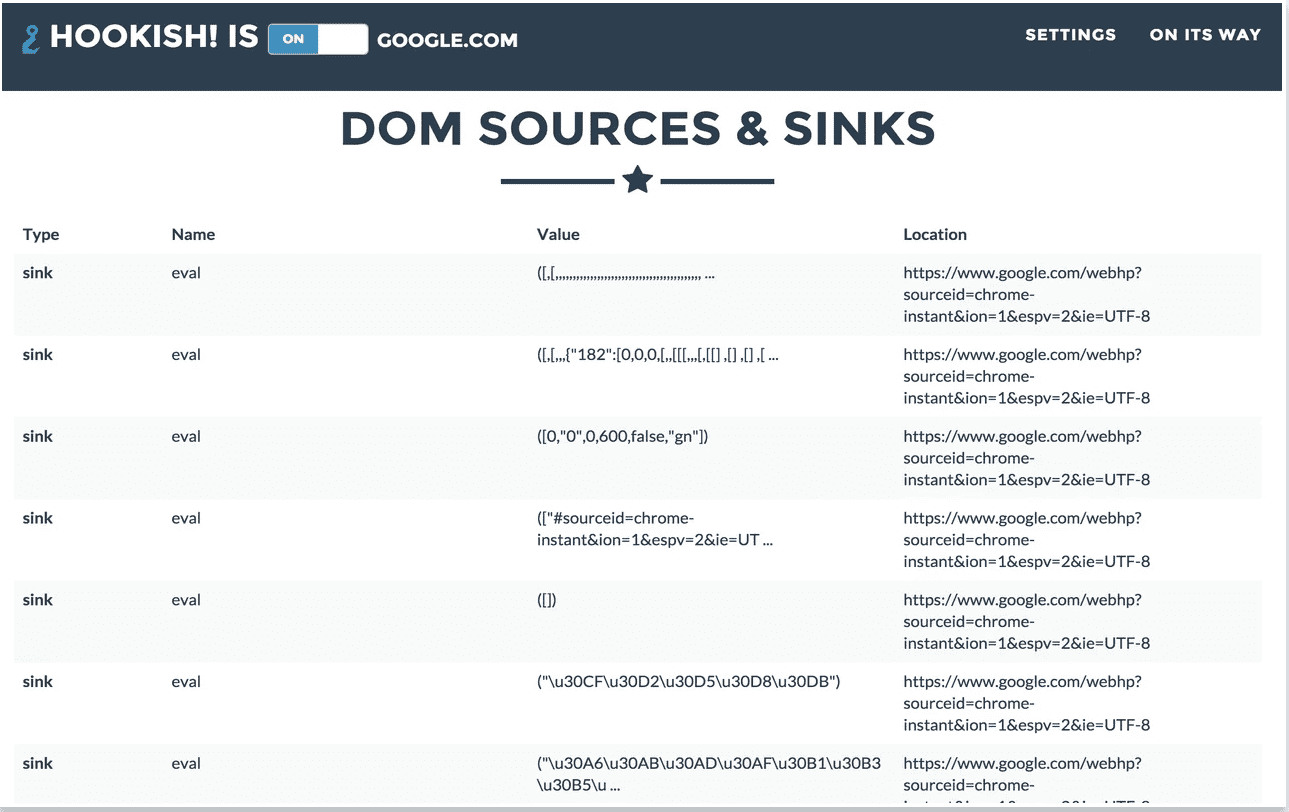
Hack Tab Web Security Tests
HackTab is a powerful web vulnerability testing app. When enabled, it watches all of the communication between your browser and the particular website (domain) which you are testing. It identifies parameters, and data types.
This allows the Chrome extension to re-create any communication between your targeted domain and your browser – testing all HTTP parameter inputs.
It only tracks requests to domains which you want to target / you are targeting, and it includes watermarks on pages it is tracking.
Current tests are as follows:
- Cross Site Request Forgery
- Reflected XSS
- MySQL Injection – sleep()
- MS SQL Injection – wait for()
- Generic SQL Injection – and 1=2
- Local File Inclusion
Videos:
Common questions regarding HackTab:
Q: Does HackTab monitor all of my web traffic?
A: No. HackTab ONLY monitors traffic to domains you target in it’s configuration and ONLY when enabled
Q: Does HackTab scan the site when I target it?
A: No. HackTab only sends tests for the parameters you target and only sends the tests that you have selected when you scan that single parameter. All tests are manually triggered.
Q: Where are the tests run from?
A: The tests are run directly from your web browser.
Q: What permissions does HackTab require?
A: HackTab requires permission to send HTTP requests to targeted domains and also read the responses from those targeted domains.
Q: Does HackTab store any information about vulnerabilities?
A: No. All site data is stored in your local Chrome extension. HackTab uses Google Analytics to store usage data. This includes number of tests run and which features users are using. No site information or identifying information is used or stored anywhere outside of your web browser.
HPP Finder
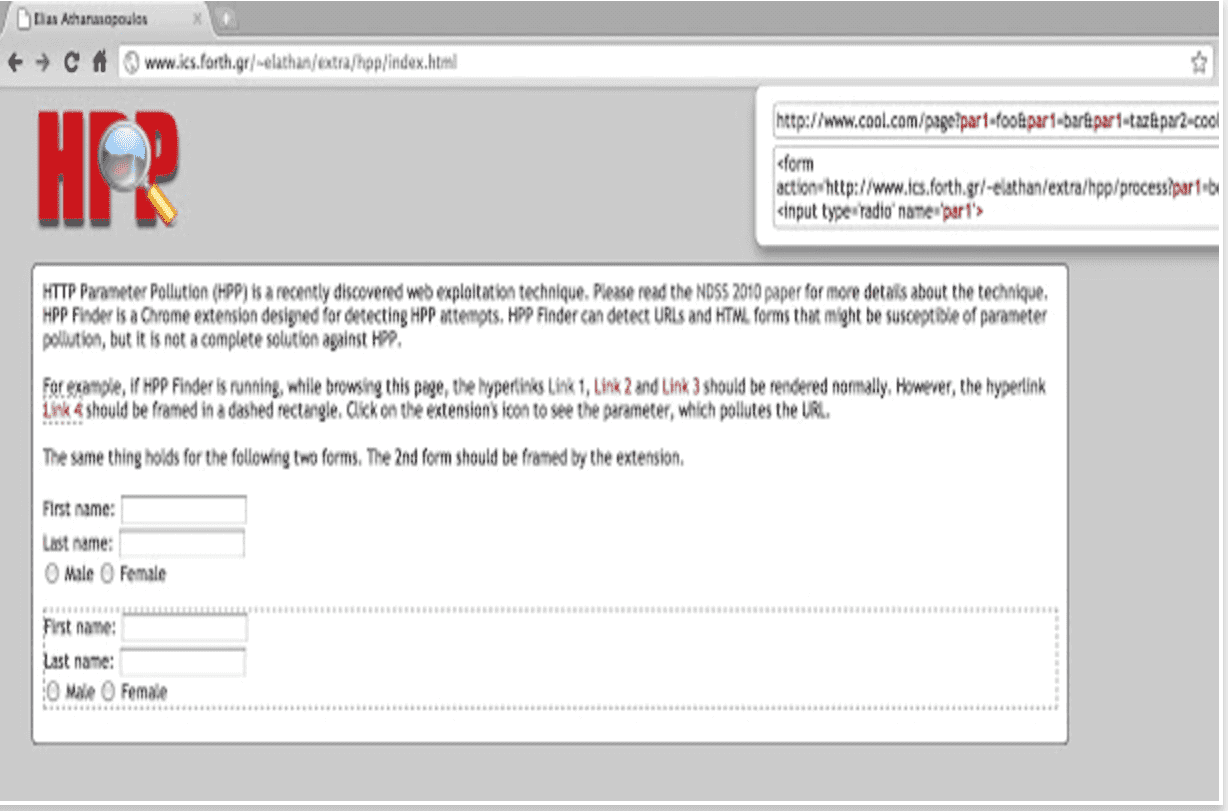
HTTP Parameter Pollution also known as HPP is a web exploitation technique. HPP Finder is a Chrome extension designed for detecting HPP attempts. It can detect URL’s and HTML forms that might be susceptible of parameter pollution, but it is not a complete solution against HPP.
You can install it from the Chrome store. Click here and it will take you the page.
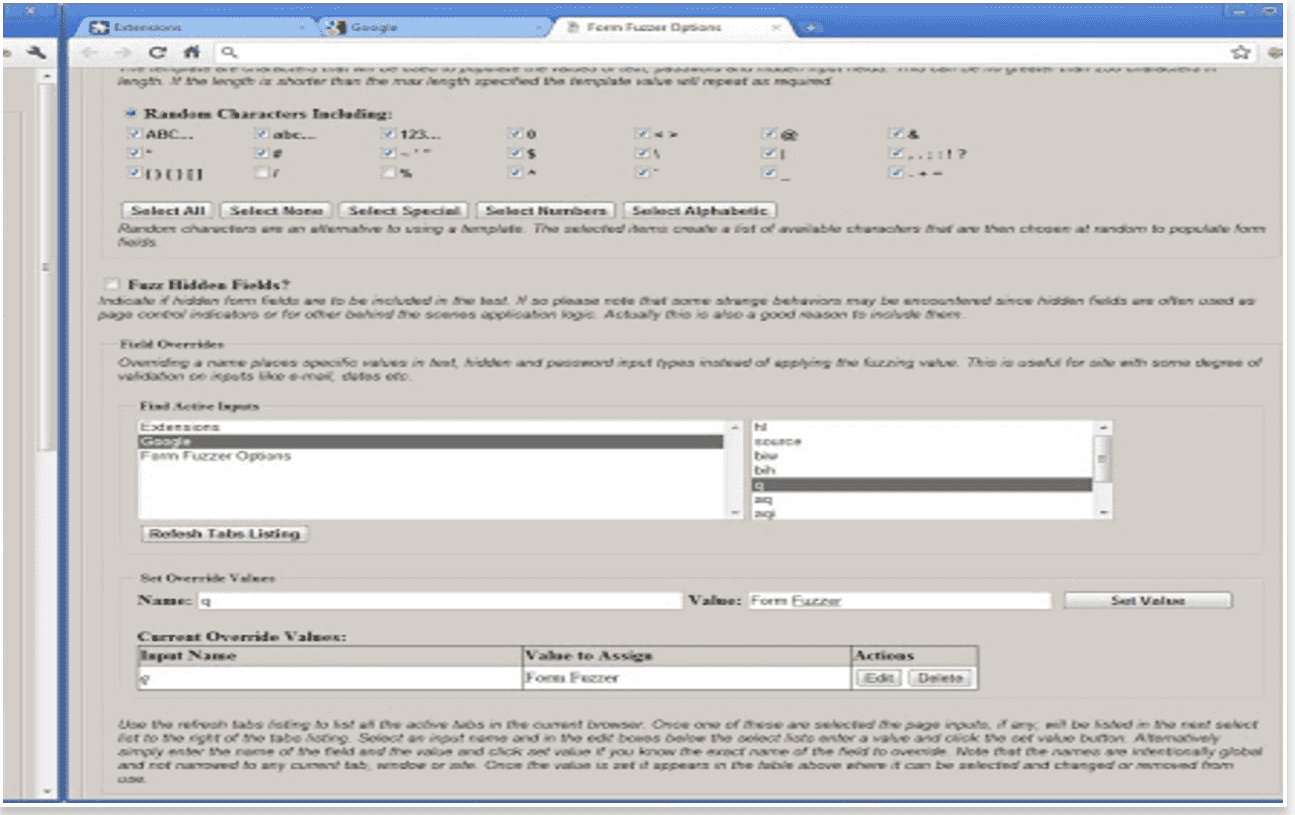
Form Fuzzer
Site Spider
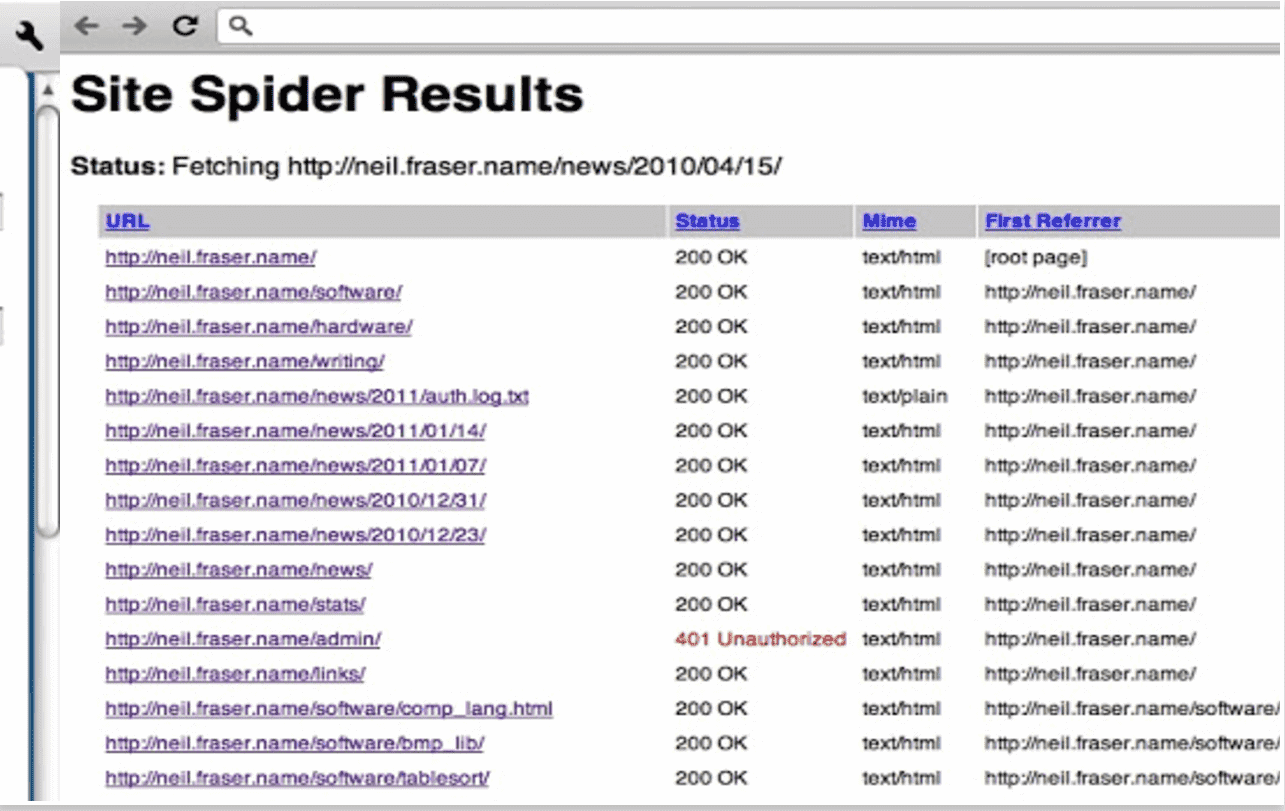
You can use this useful extension to spider websites, looking for dead links. You can restrict the Site Spider to a domain, directory, or any other regular expression.
Usage:
- Install the plugin.
- Go to the page you want to start from.
- Click the spider icon in your toolbar.
- Set the restriction regular expression and go.
- To cancel a spidering session before it has finished, just close its results tab.
Google Hack Data Base
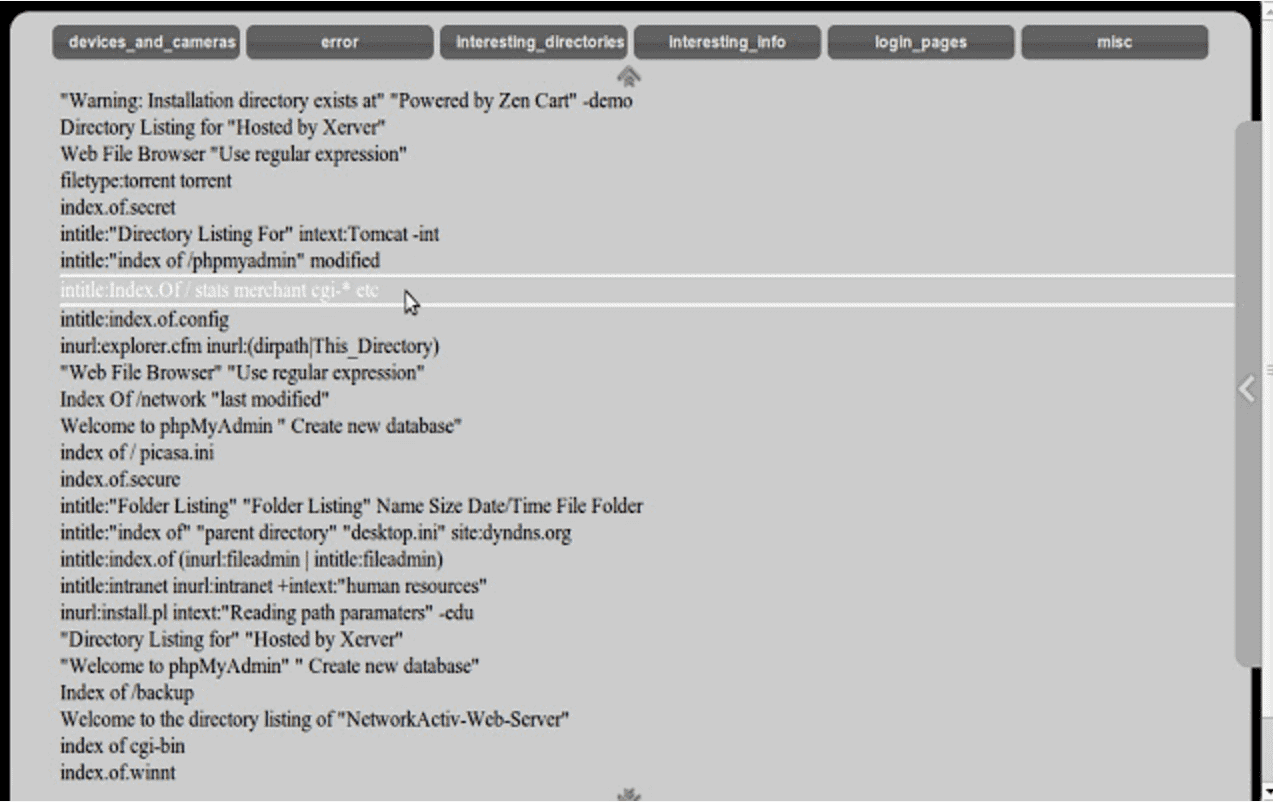
It works with with GHDB.
Basic usage:
- Choose a category
- Click on Necessary query
- To find the description click on “Search on www.exploit-db.com”
What is nice about it, is: it allows you to search for vulnerabilities on a specific website. All you have to do is, click on the search button and input the website name. With this application, you will have better basic knowledge of web security.
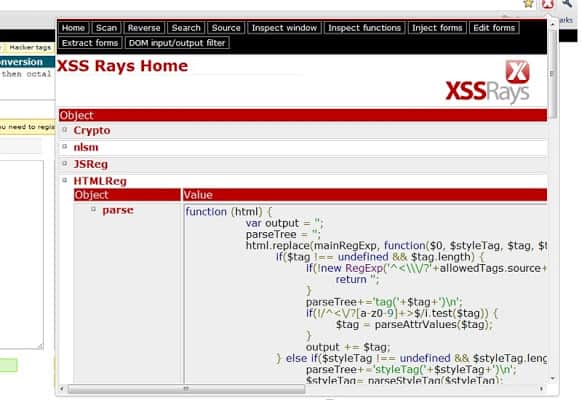
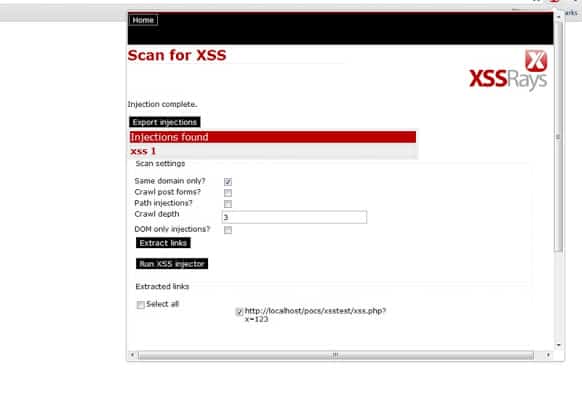
XSS Rays
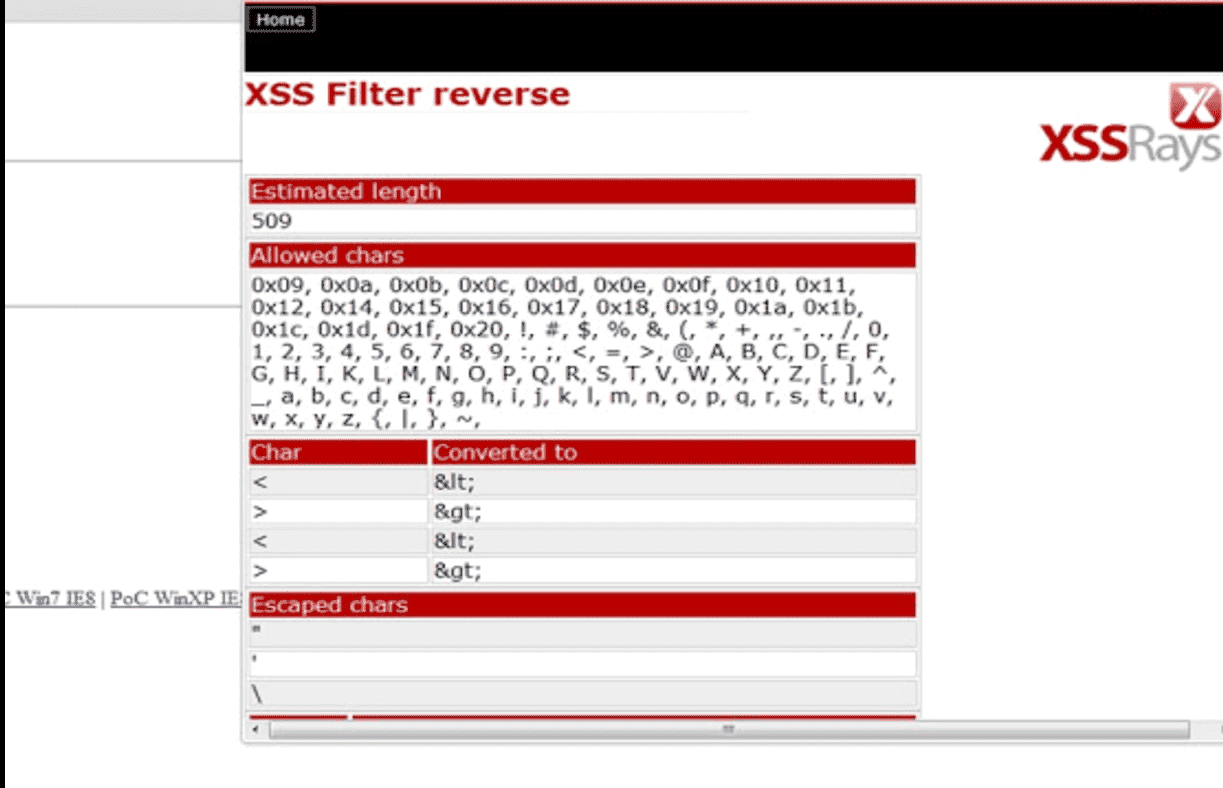
With XSS Rays you can pen test large websites. Core features are as follows:
- XSS Scanner
- XSS Reverser
- Objectioon inspection
It also has filters which you can use.
Screenshots:
Shodan
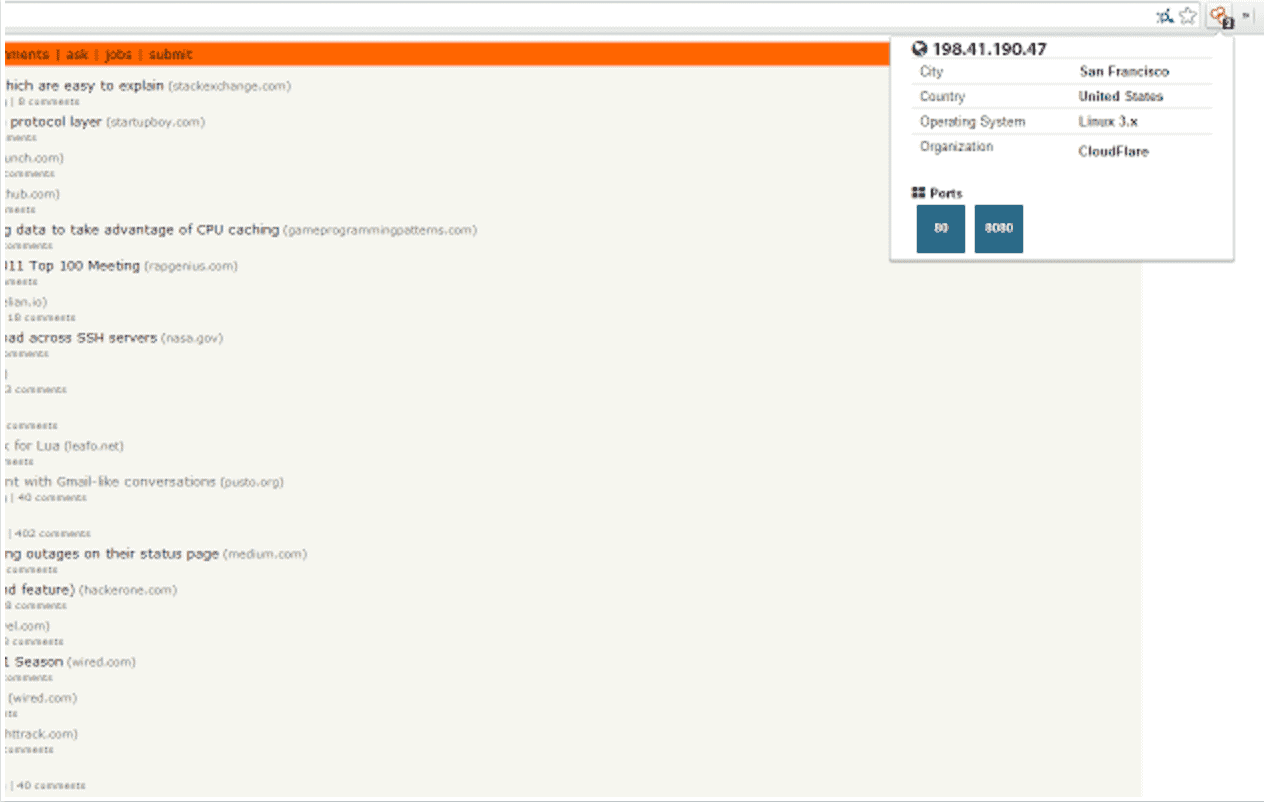
Shodan automatically checks information about a particular website, it’s IP, open ports, FTP, SSH, DNS, or maybe some unusual service which is running. The extension can see the information Shodan collected on a domain / website.
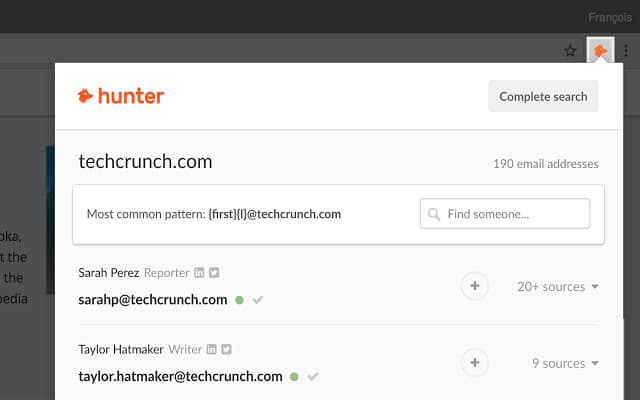
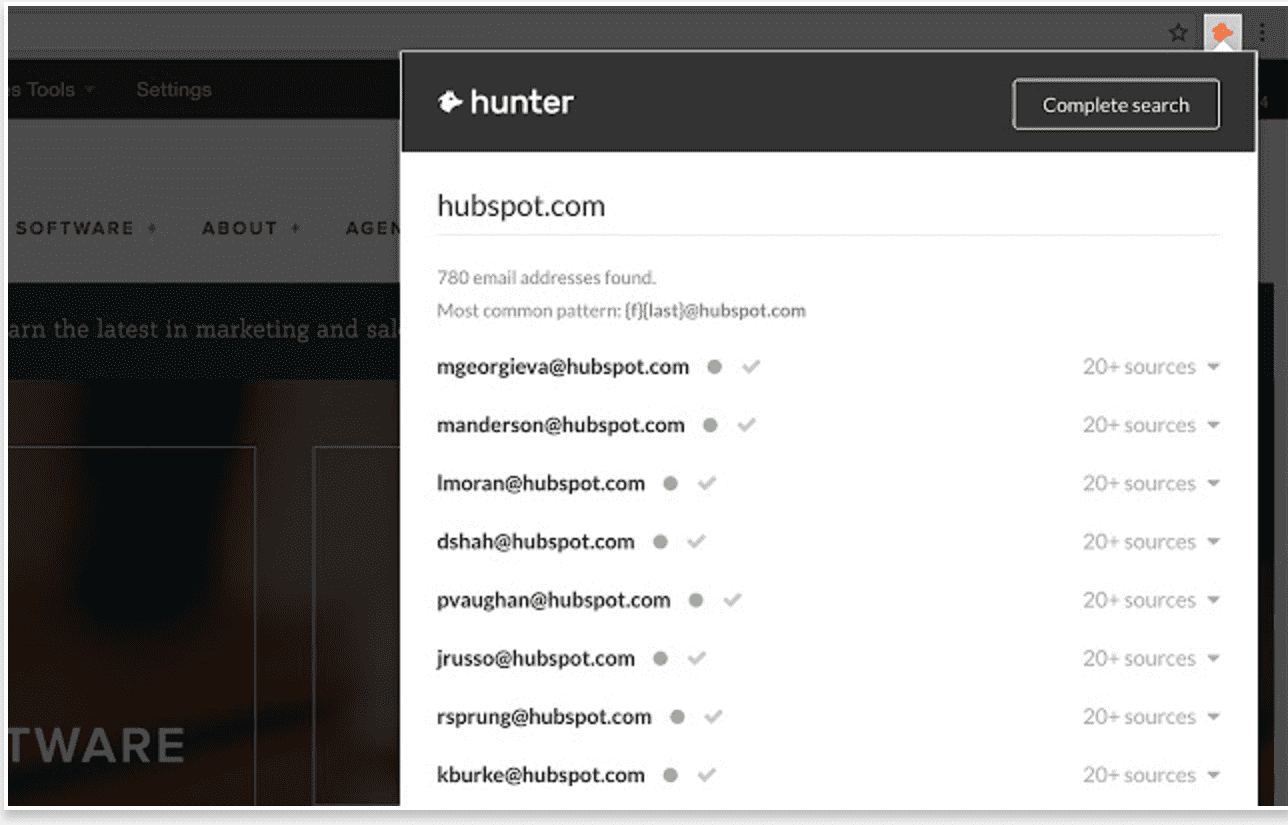
Hunter lets you find the people behind a website and their email addresses. When you click on the icon, you get a list of people with:
– Names
– Professional email addresses
– Social networks
– Job titles
– The public sources where this data has been collected
All the email addresses are returned with a quality score that evaluates the confidence they are accurate.
Features
- Get email addresses from any website: when you are on a website, click on Hunter’s button in your browser to get every email addresses we found related to the website.
- Find email addresses on LinkedIn profiles: when you visit a profile on LinkedIn, click on the button in your browser to find the email address of this profile in seconds.
- Save your leads from LinkedIn search pages and profiles. You can download all your saved leads in CSV or automatically synchronize them with Salesforce, Pipedrive, Zoho CRM, Hubspot or hundreds of other apps through Zapier.

Leave a Reply